Are you the one who holds a strong Brand image via leveraging the competency of your mobile app that has been featured on App Store? However, do you know, it will take only a time of an eye blink to get ruined that brand image if you have not applied preemptive security majors?
Even a popular app may die a slow if the user does not find it secure enough. Mobile app security or secrecy is the primary stroke that every app developers should hit while performing mobile app development course.
Let suppose a user wants to do monetary transaction within an app and he/she has to mention the bank account details, OTPs, other security details, but if there is, a chance of data loss in the app, then there is no reason left for the user to use that app again.
Some first mobile app’s data breach cases are there that we have seen in a few couples of years back…
“The very renowned or diversely using Facebook (the whole world in itself) admitted that the security breach compromised around 50 million users. Well, the company CEO has not seen the accounts getting compromised or nor found any illegal activities. However, later, Zuckerberg confirmed that the hackers users Facebook developer APIs for getting data. The data was comprised of names, genders, localities, which were linked to the user’s profile.”
Another very famous app which we use in our daily lives as on-demand services- “Uber.” Yes, right, there were some conflictions with Uber also.
“Uber had already faced allegations and was infamous for compromising user data back in 2016. They even paid £133m to settle the legal penalisation owing to the cyber-attack which happened to expose 57 million customers and driver data.”
However, app developers can wash this via performing some preemptive majors to secure the user’s sensitive data and avoid data leaks in apps. Developers must be aware of the security measures to be taken while developing a mobile app.
Table of Contents
Must perform preemptive majors to secure sensitive data in mobile apps:
Here are some of the preemptive majors to secure user’s sensitive data in App development that should be performed by every app developers before walking on the success/security path of app development.
Token-Based Authentication of APIs
A token is a bit of data that has no significance or use on its own, yet combined with the right tokenization system, turns into an indispensable player in verifying your app.
Token-based authentication works by guaranteeing that each request to a server is joined by a signed token, which the server verifies for authenticity and at precisely that point respond to the request.

There are some very vital aspects when choosing token-based authentication of APIs. The main reasons for the tokens are:
- Mobile app ready
- Pass authentication to other apps
- Extra security
- Stateless & Scalable
While developing an app, a mobile app developer must use Token-based authentication of APIs so that they can provide extra security and can prevent the app from data loss.
Encryption of Sensitive Data While Storing In Database
A standard affirming principle with sensitive data is that at same point, your server will be compromised. Considering that, in mobile app development, it’s a smart thought to secure your data, and all the more imperatively your user’s data, from a server breach.

Storing user’s passwords or credit card data in a database in plain text is a major issue. It sounds like the presence of mind that you’d encrypt that data yet very frequently it’s left wide open or feebly encrypted. Frail encryption isn’t much superior to no encryption. To the naked eye you can’t peruse the data, but if the hacker can download the encrypted data, they have a lot of time to split the encryption later on.
Every mobile app developer should channelize Encryption- to store sensitive data in the database as- Encryption uses algorithms that turn plain text into unreadable, jumbled code, ensuring an app’s secrecy. For the decryption of this ciphertext, an encryption key is required, and the key is something that only authorized people to have in their possession.
Implementing SSL
90 % of people are using Smartphones and the time they have spent on their phone was on apps. You know why an app? Because they feel secure, while using the app and do not think twice before giving these apps access to such confidential data. That is the place where the responsibility of the app developers comes into play. To keep this trust of users, developers must implement every possible technique to protect user’s data. And trust me, SSL certificate is the best way to attain that.

In a way to mobilize user’s data security, while developing an app, implementing SSL could be one of the major preemptive. Before writing any code, there are a few decisions a developer need to make from the certificate he uses to pinning to what he does when things go wrong or security breach.
SSL( Secure Socket Layer) that ensures encrypted client-server communication over HTTP-specified by HTTPS (HTTP over SSL). The encryption is based on Public Key Infrastructure and a session key. The Session key was launched because encrypting & decrypting a public or private key uses a lot of processing power.
SSL certificate acts as an impenetrable armor for mobile apps that leaves decidedly fewer possibilities of MITM attacks.
Implementing CDN
While developing an app that uses any live data, each time the app loads on someone’s device that makes a call to your server to grab the data. A huge download holding app also suffers from loads of server request that cause chances of data drain or data leaks.
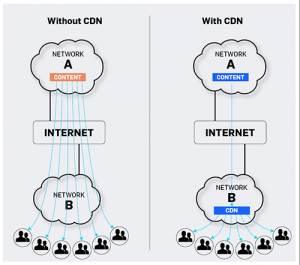
To remove this issue, developers should go for CDN (Content Distribution Network) is an easy way to develop hugely secure and scalable apps as it will mitigate the load away from the server by mirroring content to a global network of servers.
This in addition to the fact that it allows you to scale up, yet it additionally accelerates the experience for the end users as the data is dismantled from an location near them.
Using CDN as a security mask, one can make their app safe for the future as well.
Implementing Firewall
In the era where almost every hand is occupied with Smartphones and every Smartphone is occupied with lots of apps, there is a challenge for app developers to protect apps from unwanted threats or attacks.

Developers could remove these threats via implementing a firewall in their app development process. Must be thinking what is firewall? Let me tell you; an app firewall is a form of firewall that controls input, output, and access from, to, or by an app or service.
Implementing Firewalls could save the users data by blocking the unwanted inputs, outputs or system service calls.
By implementing firewalls, only users within the firewall can access particular data, or those outside the firewall have limited capabilities to the user or modify the data. Implement a setup of firewalls into your app and protect the user’s data against attacks.
Conclusion:
All the efforts and money put into the mobile app development would vanish if the users were not assured that their personal data would remain safe. Several steps need to be taken to ensure app security.
RipenApps Technologies is a top mobile app development company that believes in providing quality along with security so that our valuable customers would never fall down or never get compromised with their brand image. For more details, hit on [email protected]








 India
India USA
USA Australia
Australia Canada
Canada UK
UK UAE
UAE